There has been a surge in blockchain adoption across many industries. The revolutionary blockchain technology stores pacts of data by time-stamping making it secure. There are myriad use cases and the companies leveraging the technology are witnessing security and transparency in the processes.
Blockchain nodes are the ones that control the security of a blockchain network. The blockchain nodes have a high amount of critical data and are the target for attackers. The blockchain typically stores the data by cryptography. The blockchain node infrastructure is essential for the blockchain to function, and then the blockchain protocols share the information through the routing protocols.
Global spending on blockchain solutions will reach $14.4 billion in 2023, a total 235% increment. The foundation of blockchain technology is a strong and secure network. But blockchain vulnerabilities and blockchain node security issues are to be seen in the recent years.
In this blog, we will understand about the function of a blockchain node, the blockchain attack vectors, and specific blockchain node security issues. Further, a few measures to keep the blockchain node safe from attacks and vulnerabilities.
What the Blockchain Nodes do
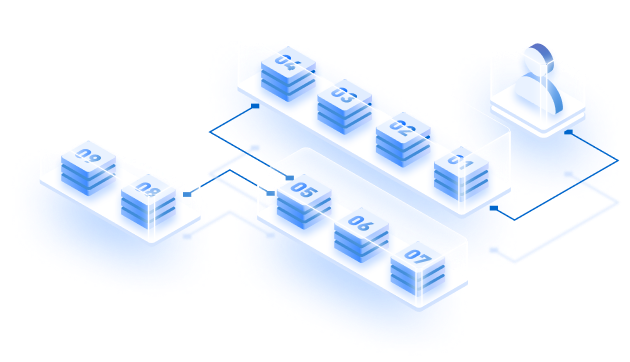
Nodes run on infrastructure resources and can be cloud-native, on-premise, or a combination of both. The nodes are the ones on which the blockchain is implemented. In the blockchain technology, there is a block that consists of all the data and has a timestamp. The blocks are arranged in an order forming a chain hence the name “Blockchain.”
The blockchain is interlinked with each other by hashes. When the new block is created, it is broadcasted onto real-world computers called nodes. The nodes are responsible for maintaining the integrity of the network. The security of the blockchain node is significant as it maintains the copies of transactions.
Blockchain Node Attack Ronin
Ronin, an Ethereum sidechain built on an NFT play-to-earn game, allowed users to transfer ETH assets to and from the platform. In March 2022, the hackers, identified as Lazarus, obtained the private keys of the bridge validator nodes. The hackers were able to get control of 5 out of 9 keys. After that, the hacks controlled the gaming platform for over a week. The attack could happen because of Sky Mavis gave control to the third-party validator. Unfortunately, due to the backdoor access the hackers were able to steal $625 million.
Blockchain Node Attack Vectors
There isn’t a perfect list of the attack vectors and many weaknesses that make the blockchain network vulnerable. Although the most important ones are:
DDoS Attacks
In a distributed denial of service (DDoS) attacks, the hackers bring down the server related to processing. This is done by consuming resources with multiple requests. The blockchain uses DDoS botnets, and thus the application layer is prone to hackers.
The most visible symptom of a DDoS attack is the site becoming slow or sometimes unavailable. Further, there are performance issues that only traffic analytics tools can analyze. In a DDoS attack, there can also be a suspicious amount of traffic from a single IP range or IP address.
Transaction Malleability Attack
Ever received a notification of “transaction unsuccessful,” and in a hurry, you paid one more time? Similarly, in this attack, the victim is lured into paying twice. The transaction on the blockchain network has a transaction ID called the hash. The attackers replace the transaction’s ID and broadcast the transaction with the altered hash. The bad actors get the altered hash confirmed before the actual transaction.
The sender is left confused as they receive the failed transaction message while the money is withdrawn from the account. To counter the problem, Bitcoin introduced SegWit to separate signature data from Bitcoin transactions and replace it with the non-malleable hash.
Malware
Like any software, the blockchain can also be subjected to various malware. The malware affects the activity on the network. Public key cryptography is used to sign transactions digitally. The malware traces these public keys or sometimes even the private keys, thus leaving the system vulnerable.
Mining malware
The malware uses the computing power of an unsuspecting node to mining. The blockchain nodes communicate with other nodes to manage transactions. The malware targets the transaction to block the node.
6 Blockchain Node Security Issues
The nodes employ the private and crypto encryption keys to create a new block. However, several issues specifically affect the blockchain nodes only. The major blockchain node security issues are a few of the below-mentioned points.
51% attacks
This attack mainly occurs in the initial stages of the chain; the concept is to gain control over 51% of the mining power. By gaining 51% of the power, the bad actors can control the transactions and re-write the chain portions. The hackers get the power to fork new chain and allow unlimited spending.
Sybil attacks
This attack happens when the attacker creates multiple fake nodes in order to initiate the 51% attack. Several identifiers are assigned to the same node. The hacker takes control of the multiple nodes of the blockchain network. When the hacker takes control of the various nodes, the victim is surrounded by fake nodes. The Sybil attack can be prevented by increasing the cost of creating a new identity.
Routing attack
In such attacks, hackers divide the data over a group of network nodes. This further prevents the chain from reaching a consensus. These protocols have vulnerabilities and alter the chain state. The routing attacks comprise two attacks — partition attack and delay attack. The former intercepts the network into two parts, and the delay attack tampers with the messaging on the network.
Timejacking
In this attack, the malicious attackers change the network time counter of the node and force the blockchain node to acquire a different blockchain. The malicious actors add many fake peers with inaccurate timestamps. To prevent timejacking the time acceptance can be restricted.
Eclipse attacks
The attacker controls a large number of IP addresses and then overwrites the addresses. These nodes with overwritten addresses are restarted, and all the outgoing transactions reach the IP address controlled by the attacker.
Vector76
In this, the attacker creates two nodes, of which one node is connected to the peers on the blockchain network while the other is connected with the exchange node. The attacker does two transactions, a high-value, and a low-value. Then attacker holds the high-value transaction block from an exchange. Later, the attacker receives the high-value transaction by dodging the system.
7 tips on How to Protect the Blockchain Node
Few of the basic steps to ensure the safety of the blockchain node and the overall infrastructure:
- Keep the software up to date and review the configurations. There should be an assessment of the common vulnerabilities.
- The use of an antivirus to detect any malware in the nodes. Further, one can employ the web application firewall to protect the infrastructure.
- There should be constant monitoring of pools and an alert if there is a surpass on the limit of 40% miners. Therefore, send the remaining miners to other pools.
- The security routing protocols come in handy to counter-routing attacks. Perform rigorous verification, authorization, and authentication.
- Smart contracts are more sensitive to attacks; thus, it’s essential to check the smart contracts for any vulnerabilities.
- Penetration tests and security audits on the blockchain network make the infrastructure more robust. Use multi-factor authentication whenever possible.
- Deploying end-to-end encryption is essential to ensure better privacy on the network. Use load balancers to distribute the traffic on the network.

When we talk about the blockchain overall security there are several factors that contribute to it such as consensus and immutability. The cryptography on the network secures the information from the third parties. Further, there are public and private keys along with signatures to secure the network. Lastly, using the quantum computers and quantum-resistant blockchains stoves many of the security related issues.
Final Thoughts
Organizations, institutes, and individuals opting for blockchain technology should not take security for granted. Hackers keep finding different ways to breach the network. Thus, it is necessary to take corrective measures and opt for blockchain infrastructure management platforms.
The platforms will implement authentication and cryptography key vaults. Strong authentication and data encryption are necessary to secure the blockchain node and the network’s communication. The secure network will ensure better processing of the data and will make the technology more adaptable.
Partner with Zeeve
In a search for secure blockchain node access? Connect with Zeeve. We give the utmost importance to a blockchain node network’s unparalleled security and robust infrastructure.
We feature a robust set of APIs to build DApps for many use cases across industries. Zeeve supports Decentralized Finance (DeFi) space with decentralized storage, trusted nodes, and smart contracts.
To learn more about Zeeve, join us on Twitter and Telegram. Feel free to contact us directly.